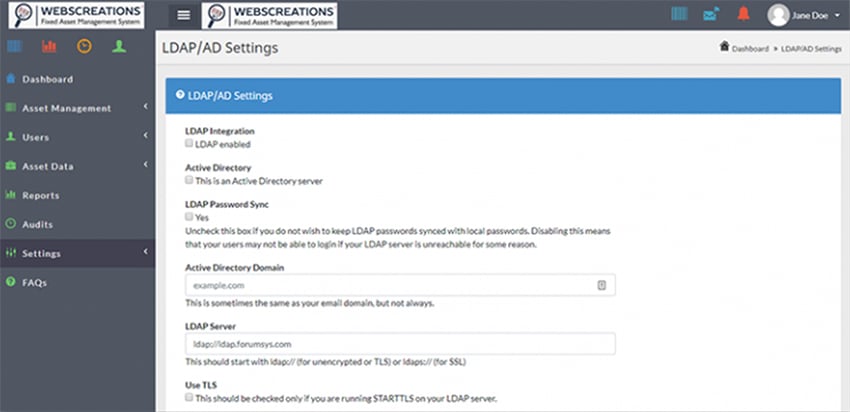
LDAP/AD
LDAP Stands for Lightweight Directory Access Protocol. It is a lightweight client-server protocol used to access centrally stored information over a network. LDAP cannot create or specify how a directory service operates. LDAP provides directory support to browser applications that do not have directory service support.
Why Use LDAP/ AD?
The main benefit of using LDAP is that it can consolidate information of an entire organization into a central repository. This central directory can be accessible from any location on the network. It supports Transport Layer Security (TLS) to provide data protection.
What is Active Directory?
Active Directory (or AD) is a directory services implementation that provides authentication functionality, group and user management, policy administration and more. As far as directory services go, Microsoft Active Directory is by far the most common in use today, in no small part because it is easy to use, secure, provides single sign on and works well in business environments or over VPN.
How Active Directory and LDAP Work Together
Active Directory supports LDAP, meaning you can combine the two to help you improve your access management. In fact, many different directory services and access management solutions can understand LDAP, making it widely used across environments without Active Directory as well.
LDAP Authentication Explained
Firstly, there are two different types of LDAP authentication; simple and Simple Authentication and Security Layer (SASL).
Let’s first take a look at simple authentication. Simple authentication allows you to authenticate via three different methods:
- Anonymous Authentication: as the name suggests, this gives anonymous status to LDAP.
- Unauthenticated Authentication: this should not grant access; it is for logging purposes only.
- Name/Password Authentication: again, as the name suggests, this grants access based on a supplied name and password.
SASL authentication links LDAP with another authentication system (such as Kerberos). Through a series of challenge and response messages, the LDAP server sends a message to the authorization service and results in either a successful or failed authorization.
An important note here is that LDAP sends messages that are unencrypted. It is a good idea to add some sort of encryption to these messages to keep your sensitive information secure from prying eyes.
LDAP Directory Service Model
The LDAP Directory Service Model is based on a client server model which consists of one or more LDAP servers containing data which makes an LDAP directory tree. The LDAP client requests information or performs operations by connecting to an LDAP server. The LDAP server performs this operation, or refers to another LDAP server that may able to perform this operation or provide information to LDAP clients.